Description
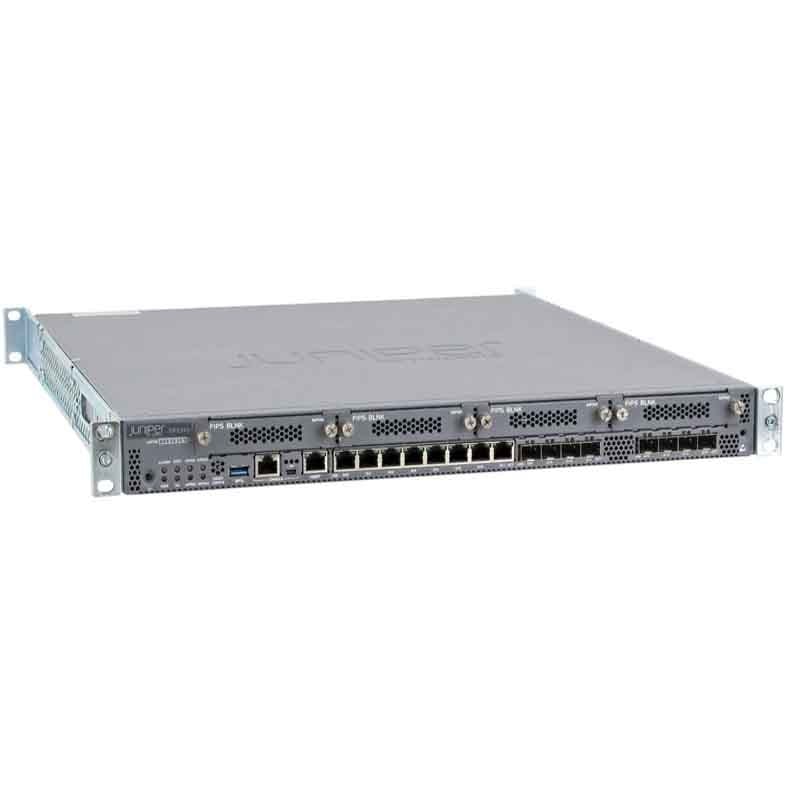
Product Overview of the Juniper SRX345 Security Gateway: A Comprehensive Guide
In today’s interconnected world, network security is of paramount importance. With the ever-evolving landscape of cyber threats, businesses, and organizations must invest in robust security solutions to protect their data and network infrastructure. The Juniper SRX345 Security Gateway is one such solution that stands as a fortress against potential threats. In this comprehensive guide, we will explore the features, applications, and significance of the Juniper SRX345, a Small Form-Factor Pluggable (SFP) Gateway Security Transceiver, boasting 8×1 Gigabit Ethernet (GbE) ports, 8G Flash, and 4x Modular Port Interface Modules (MPIM) Firewall Appliance.
Features of the Juniper SRX345 Security Gateway
Before we delve into the specifics, let’s introduce the key elements that make the Juniper SRX345 a noteworthy security gateway.
Small Form-Factor Pluggable (SFP) Gateway
The Juniper SRX345 features a Small Form-Factor plugable (SFP) transceiver, which is known for its versatility in network connectivity. SFPs are modular transceivers that can be easily plugged into a compatible port, allowing for flexibility and adaptability in network configurations.
8×1 Gigabit Ethernet (GbE) Ports
The gateway is equipped with 8×1 Gigabit Ethernet (GbE) ports. These high-speed ports are crucial for fast and reliable data transfer, making them suitable for businesses with substantial data traffic and bandwidth requirements.
8G Flash
With 8 gigabytes of Flash storage, the Juniper SRX345 has ample space to store essential data and configurations. This storage capacity is essential for maintaining logs, updates, and other critical information.
4x Modular Port Interface Modules (MPIM)
The Juniper SRX345 is armed with 4 Modular Port Interface Modules (MPIM). These modules are essential for enhancing network connectivity, allowing for the integration of various interfaces and technologies. They provide flexibility in adapting to different networking needs.
Firewall Appliance
As a firewall appliance, the Juniper SRX345 plays a critical role in protecting your network from cyber threats. It acts as a barrier between your internal network and potential external threats, ensuring that unauthorized access and malicious activities are blocked.
The Significance of the Juniper SRX345 Security Gateway
Now that we’ve introduced its features, it’s time to explore why the Juniper SRX345 is a pivotal player in the realm of network security.
Versatile Connectivity
The SFP transceiver and 8×1 Gigabit Ethernet (GbE) ports provide versatile connectivity options. This versatility is essential for organizations that require different types of connections for their network infrastructure.
High-Speed Data Transfer
The presence of 8 Gigabit Ethernet ports ensures high-speed data transfer. This is vital for businesses that rely on seamless data communication, real-time applications, and multimedia streaming.
Abundant Flash Storage
The 8G Flash storage capacity is essential for storing essential data, configurations, and logs. It ensures that your security gateway can efficiently handle the data generated and maintain a record of network activities.
Modular Port Interface Modules (MPIM)
The presence of 4 MPIM modules offers flexibility and adaptability. These modules allow businesses to integrate different interfaces and technologies into their network setup, making it easier to adapt to evolving networking needs.
Robust Firewall Protection
As a firewall appliance, the Juniper SRX345 acts as the first line of defense against cyber threats. It helps in detecting and blocking unauthorized access, ensuring that your network remains secure.
Key Features of the Juniper SRX345 Security Gateway
Let’s take a closer look at the key features that make the Juniper SRX345 Security Gateway a standout choice for network security.
SFP Transceiver
The Small Form-Factor Pluggable (SFP) transceiver offers versatility in network connectivity. It allows for the integration of various optical and copper interfaces, providing flexibility in network configuration.
High-Speed Gigabit Ethernet Ports
The presence of 8×1 Gigabit Ethernet (GbE) ports ensures high-speed data transfer, making it suitable for businesses with substantial data traffic and bandwidth needs.
Ample Flash Storage
With 8 gigabytes of Flash storage, the Juniper SRX345 can efficiently store logs, updates, and essential data. This storage capacity is vital for maintaining a record of network activities.
Modular Port Interface Modules (MPIM)
The 4 Modular Port Interface Modules (MPIM) enhance network connectivity by allowing for the integration of various interfaces and technologies, making it easy to adapt to different networking requirements.
Firewall Capabilities
As a firewall appliance, the Juniper SRX345 acts as a protective shield for your network. It helps in blocking unauthorized access and malicious activities, ensuring the security of your network.
Practical Applications of the Juniper SRX345 Security Gateway
To understand the real-world utility of the Juniper SRX345, let’s explore the scenarios where it plays a crucial role in network security and management.
Small and Medium-Sized Businesses
Small and medium-sized businesses benefit from the versatility of the Juniper SRX345 in network connectivity. It provides the high-speed data transfer required for modern business operations.
Data Centers
In data centers where high-speed data transfer is essential, the Juniper SRX345 acts as a security gateway, ensuring that data remains secure while being transferred efficiently.
Educational Institutions
Educational institutions handling substantial data traffic, online learning platforms, and multimedia-rich educational content can count on the Juniper SRX345 for robust network security.
Healthcare
Healthcare organizations dealing with sensitive patient data rely on the Juniper SRX345 to ensure the confidentiality and integrity of their network.
Government Agencies
Government agencies must protect critical data and sensitive information. The Juniper SRX345 provides the security required to safeguard government networks.
Advanced Security Features of Firewall
The SRX345 is a high-performance network security device from Juniper Networks that provides Advanced security features to protect enterprise networks from various types of threats. Some of the advanced security features of the SRX345 include:
- Firewall: The SRX345 includes a stateful firewall that can inspect and control incoming and outgoing traffic based on configurable security policies. It can also support advanced firewall features such as Application Security, User Firewall, and Zones.
- VPN: The SRX345 can be configured to support various VPN protocols, such as IPsec and SSL, and can be used to create secure connections between remote users and the enterprise network.
- Intrusion Detection and Prevention (IDP): The SRX345 includes an IDP system that can detect and prevent a wide range of security threats, including network-based attacks and application-layer attacks. It can also support advanced IDP features such as Advanced Malware Protection (AMP)
- Advanced Threat Protection: The SRX345 can also detect and mitigate advanced threats such as Advanced Persistent Threats (APT) and zero-day attacks using features such as Advanced Security Intelligence (ASI)
- DDoS Protection: The SRX345 can protect against Distributed Denial of Service (DDoS) attacks by identifying and blocking malicious traffic before it can reach the network.
- Multi-Purpose Interface Modules (MPIM): The SRX345 includes four MPIM slots, which can be used to add additional hardware and software components to the device. These components can include additional network interfaces, security modules, and other hardware and software components that are designed to enhance the functionality and performance of the device.
Deployment and Scalability
The SRX345 is a high-performance network security device from Juniper Networks that can be deployed in a variety of ways to meet the specific needs of an enterprise network. It also offers scalability options to meet the changing needs of the network.
- Deployment: The SRX345 can be deployed as a firewall at the edge of the network, where it can protect the network from external threats by inspecting and controlling incoming and outgoing traffic. It can also be deployed as a VPN gateway, allowing remote users to securely connect to the enterprise network.
- Scalability: The SRX345 can be scaled up or down to meet the changing needs of the network. It can be configured with additional interfaces and security modules to support more users, devices, or traffic. It can also be deployed in a cluster or high-availability configuration to provide redundancy and failover capabilities.
- Modularity: The SRX345 includes four Multi-Purpose Interface Modules (MPIM) slots, which can be used to add additional hardware and software components to the device. These components can include additional network interfaces, security modules, and other hardware and software components that are designed to enhance the functionality and performance of the device.
- Virtualization: The SRX345 can also be deployed as a virtual instance on a hypervisor such as VMware, allowing it to share resources with other virtualized devices and applications. This can help to reduce the number of physical devices required and improve the overall scalability of the network.
General Information about the Juniper SRX345
- Manufacturer: Cisco
- Part Number or SKU# SRX345
- Product Type: Firewall Appliance
Technical Information of Juniper Security Appliance
- Form Factor:1U
- Total Onboard Ports:16X1GBE Security Appliance
- Onboard RJ-45 Ports:8X1GBE
- Onboard Small Form-Factor Pluggable (SFP) Transceiver Ports:8X1GBE
- Macsec Ports:16x1GBE
- Out-Of-Band (Oob) Management Ports:1x1GBE
- Mini Pim (WAN) Slots:4
- Console (RJ-45 + Miniusb):1
- USB 2.0 Ports (Type A):1
- Optional POE+ Ports:0
- System Memory (RAM):4 GB
- Storage (Flash):8 GB
- SSD Slots:1
Power Description for this Juniper Firewall Appliance
- Redundant PSU: No
- Power Supply: AC (External)
- Maximum POE Power: N /A
- Average Power Consumption:27W/112W
- Average Heat Dissipation:157 BTU/H/755 BTU/H
- Maximum Current Consumption:1.364 A
- Acoustic Noise Level:35 DBA
- Airflow/Cooling: Front To Back
In summary, the Juniper SRX345 Security Gateway is a versatile and robust solution for network security and management. With its SFP transceiver, high-speed Gigabit Ethernet ports, ample Flash storage, MPIM modules, and firewall capabilities, it offers the tools necessary to protect your network and ensure efficient data transfer.
Whether you’re a small business, a data center, an educational institution, a healthcare organization, or a government agency, the Juniper SRX345 can play a pivotal role in securing your network infrastructure.
Before purchasing, make sure to consider compatibility with your existing network setup. You can acquire the Juniper SRX345 from various sources, including Juniper’s official website, authorized resellers, online retailers, and local IT suppliers.
In an era where network security is non-negotiable, the Juniper SRX345 stands as a reliable guardian for your network, ensuring that your data remains protected and your network operations run smoothly.